Documentation Index
Fetch the complete documentation index at: https://docs.flowx.ai/llms.txt
Use this file to discover all available pages before exploring further.
Overview
Microsoft Outlook is a data source type in Integration Designer that provides native Outlook connectivity through the Microsoft Graph API. Unlike the Email Trigger (IMAP) and Email Sender (SMTP) data sources, Microsoft Outlook uses Azure AD authentication and the MS Graph API for a unified read and send experience. Use cases include:- Email-triggered workflows: Automatically start processes when emails arrive in an Outlook mailbox
- Customer communication: Send emails and replies directly from business processes
- Document processing: Trigger workflows when emails with attachments are received
- Unified inbox management: Read and send from the same data source configuration
- Read Emails — monitor a mailbox and trigger processes
- Send Emails — send emails from processes via notification templates
- Read & Send Emails — both capabilities in a single data source
When to use Microsoft Outlook vs Email Trigger / Email Sender
FlowX.AI offers two ways to connect to email: Microsoft Outlook (MS Graph API) and Email Trigger / Email Sender (IMAP/SMTP). Choose based on your mail provider and requirements.| Microsoft Outlook | Email Trigger + Email Sender | |
|---|---|---|
| Protocol | MS Graph API | IMAP (read) + SMTP (send) |
| Authentication | Azure AD (client credentials) | Username + password / app password |
| Read + Send | Single data source (Read & Send scope) | Two separate data sources |
| Reply threading | Native — uses MS Graph message ID to maintain conversation threads | Manual — requires Message-ID header forwarding |
| Provider support | Microsoft 365 / Outlook only | Any IMAP/SMTP-compatible mail server |
| Best for | Organizations using Microsoft 365 | Gmail, on-premise mail servers, or mixed environments |
How it works
Register an Azure AD app
Create a Microsoft Outlook data source
Connect to processes
Creating a Microsoft Outlook data source
Prerequisites
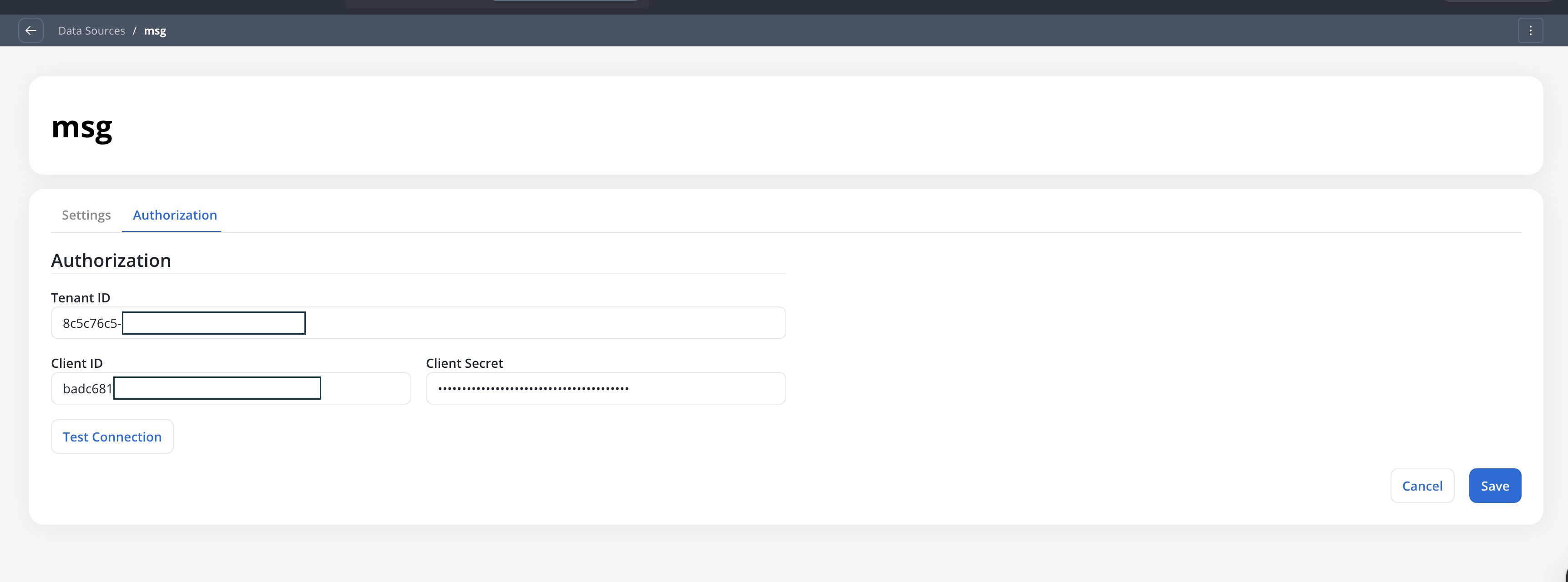
Before configuring a Microsoft Outlook data source, ensure you have:- Access to Integration Designer with appropriate permissions
- An Azure AD app registration with the required MS Graph API permissions:
| Scope | Required permissions (any one) |
|---|---|
| Read Emails | Mail.Read, Mail.ReadBasic, or Mail.ReadWrite |
| Send Emails | Mail.Send or Mail.ReadWrite |
| Read & Send Emails | One read permission + one send permission |
- Azure AD credentials: Tenant ID, Client ID, and Client Secret
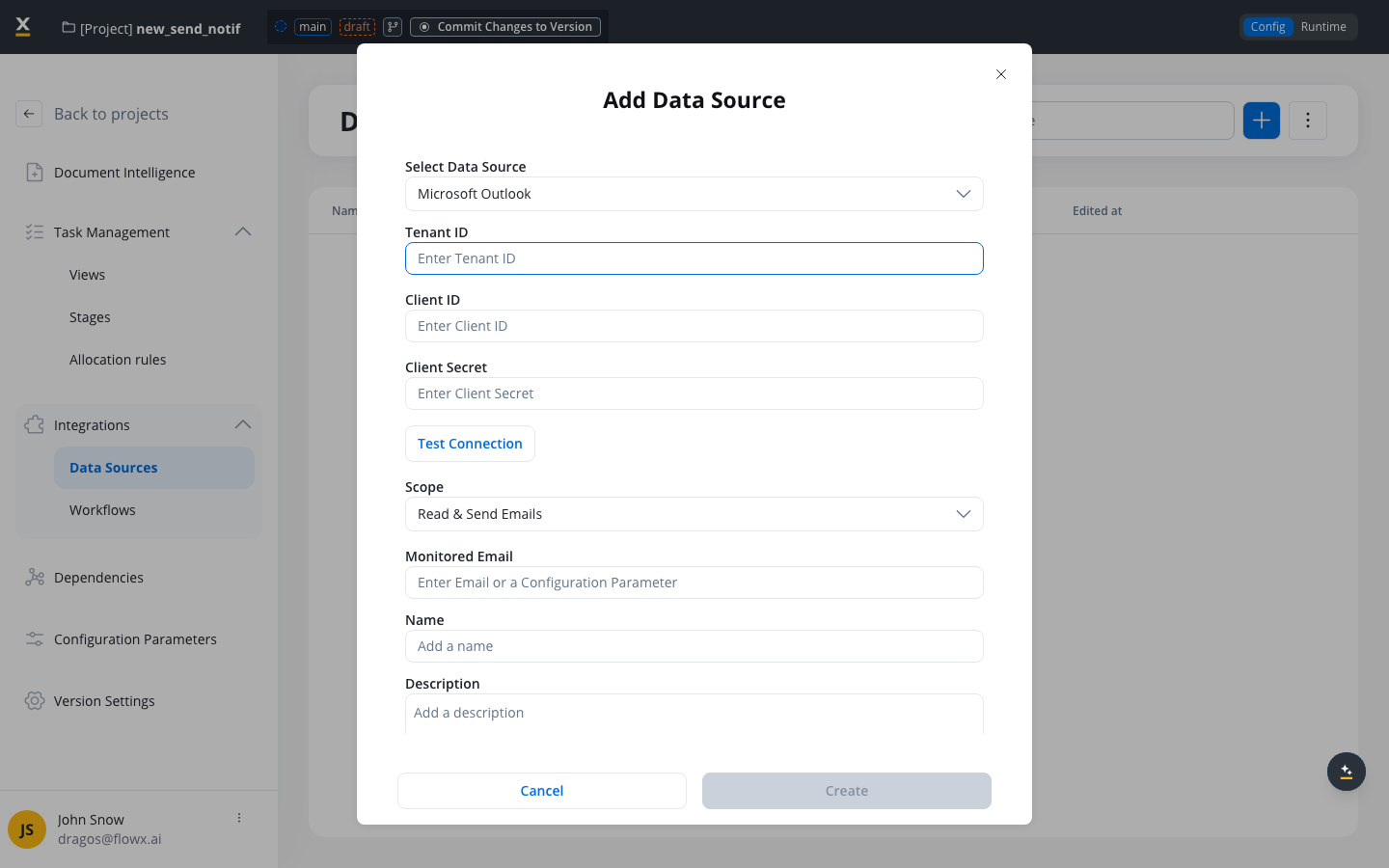
Step 1: Access Integration Designer
- Navigate to FlowX Designer → Your workspace → Projects → Your project → Integrations → Data Sources
- Click the + button to open the Add Data Source dialog
- Select Microsoft Outlook as the data source type
Step 2: Configure authentication
Step 3: Test the connection
Click the Test Connection button to verify your Azure AD credentials:| Result | Message | Action |
|---|---|---|
| ✅ Success | ”Established connection” | Proceed to configure scope |
| ❌ Error | ”Failed to establish connection” | Check Azure AD credentials and permissions |
Step 4: Configure scope and email
| Option | Description |
|---|---|
| Read Emails | Monitor a mailbox and trigger processes when emails arrive |
| Send Emails | Send emails from processes via notification templates |
| Read & Send Emails | Both read and send capabilities |
Step 5: Name and description
- Required field
- Must be unique within the project
- Only letters, numbers, and these characters allowed:
[],(),.,_,- - Minimum 3 characters, maximum 50 characters
Settings page
After creating the data source, configure monitoring and validation settings in the Settings tab. The available settings depend on the selected scope.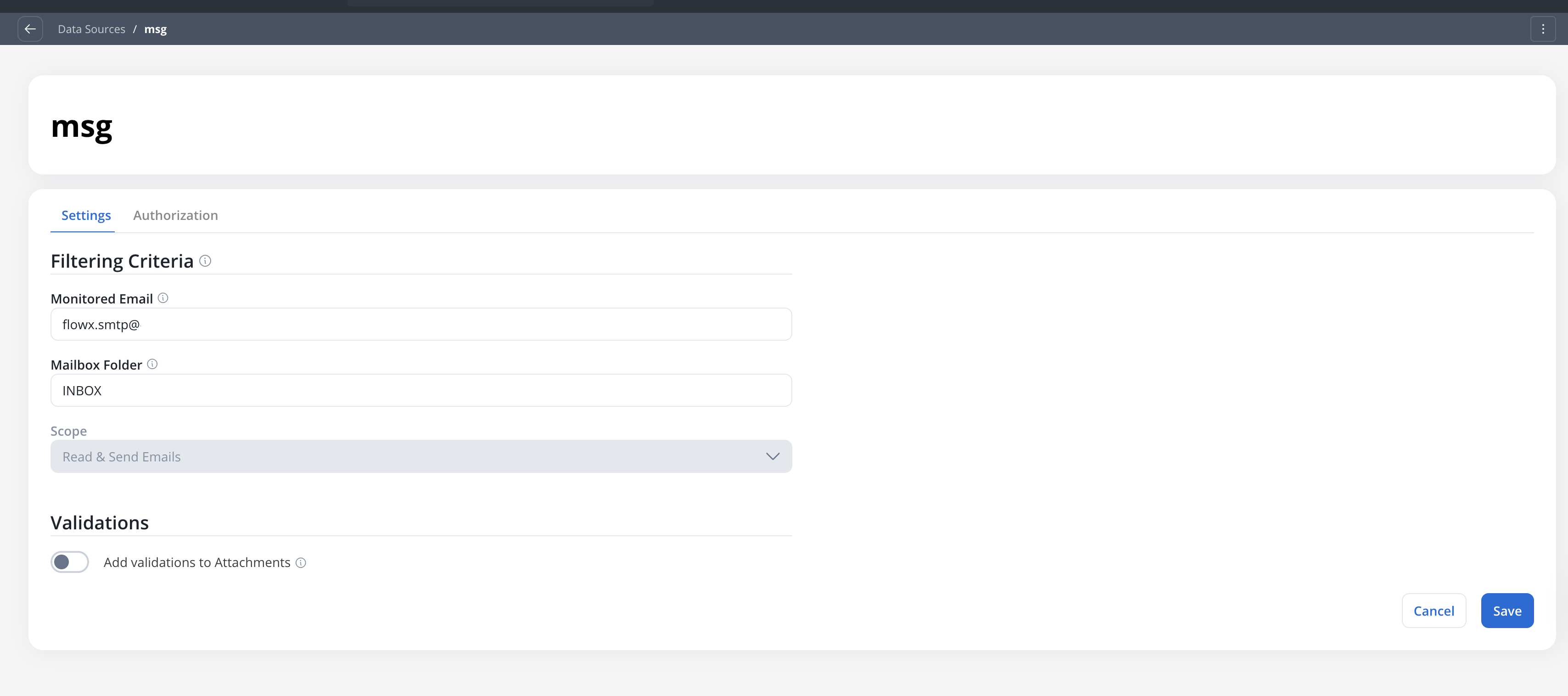
Read scope settings
For data sources with Read Emails or Read & Send Emails scope:Filtering criteria
InboxSupported well-known folder names:Inbox,Sent,Drafts,Deleted,Junk,Archive,Outbox
Attachment validations
Toggle ON the Add validations to Attachments option to configure validation rules for incoming email attachments.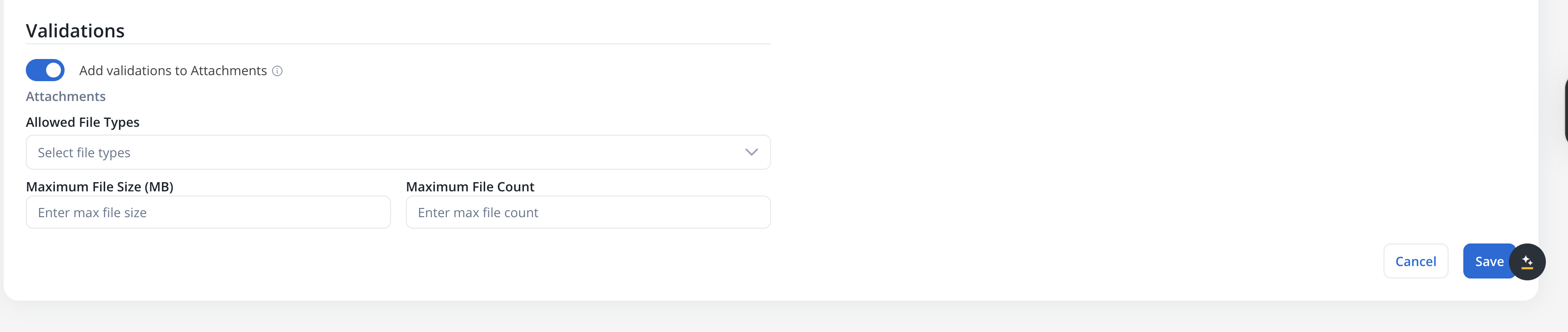
| Type | Extensions |
|---|---|
.pdf | |
| DOCUMENT | .doc, .docx, .txt |
| IMAGE | .png, .jpg, .jpeg, .tif, .tiff |
| EXCEL | .xls, .xlsx, .csv |
| ZIP | .zip |
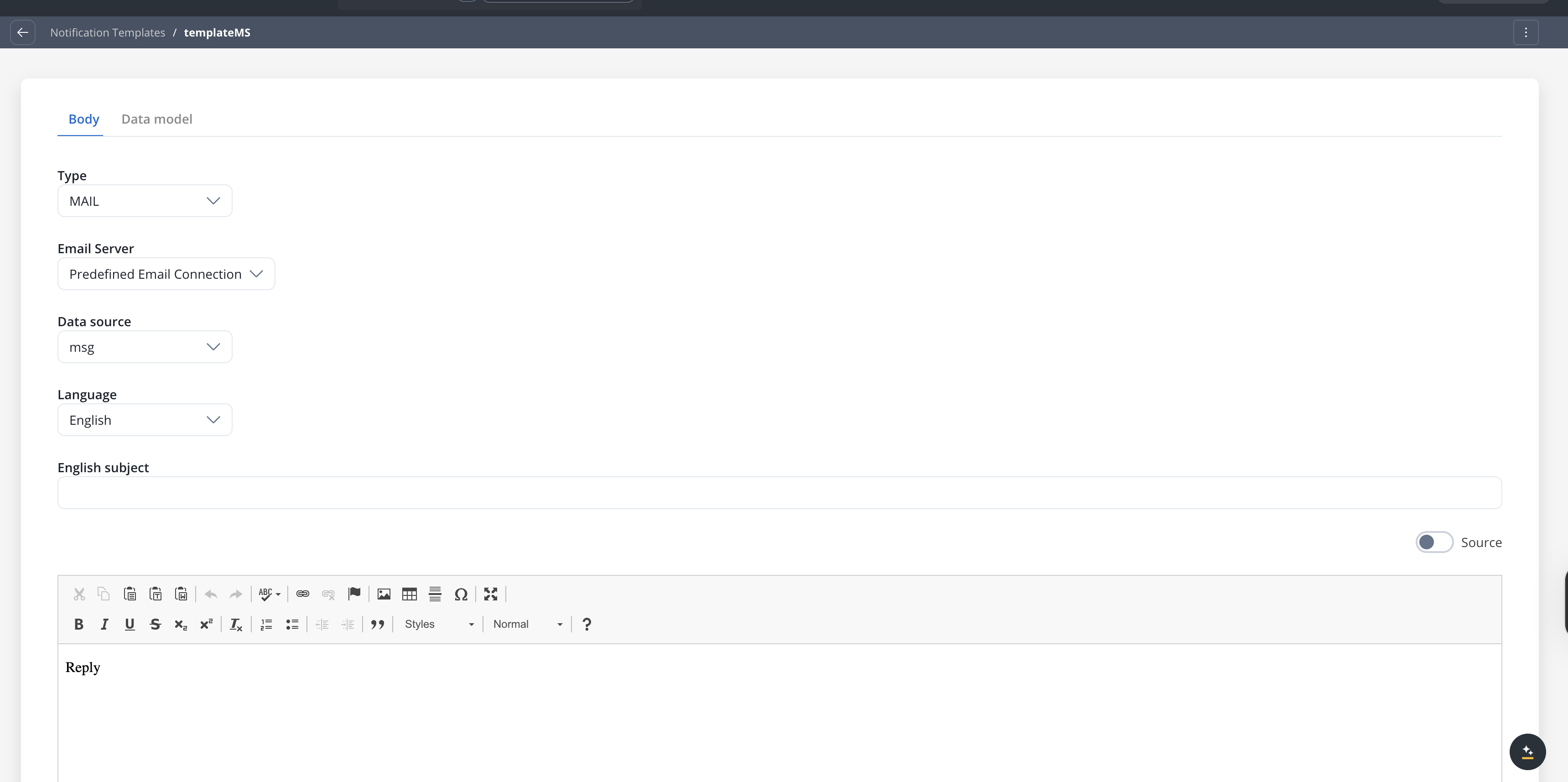
Send scope settings
For data sources with Send Emails scope only, the Settings tab shows a simplified view:Authorization page
Connecting to processes
Reading emails (process trigger)
To trigger processes when emails arrive:Configure the Message Start Event
Select Microsoft Outlook as trigger type
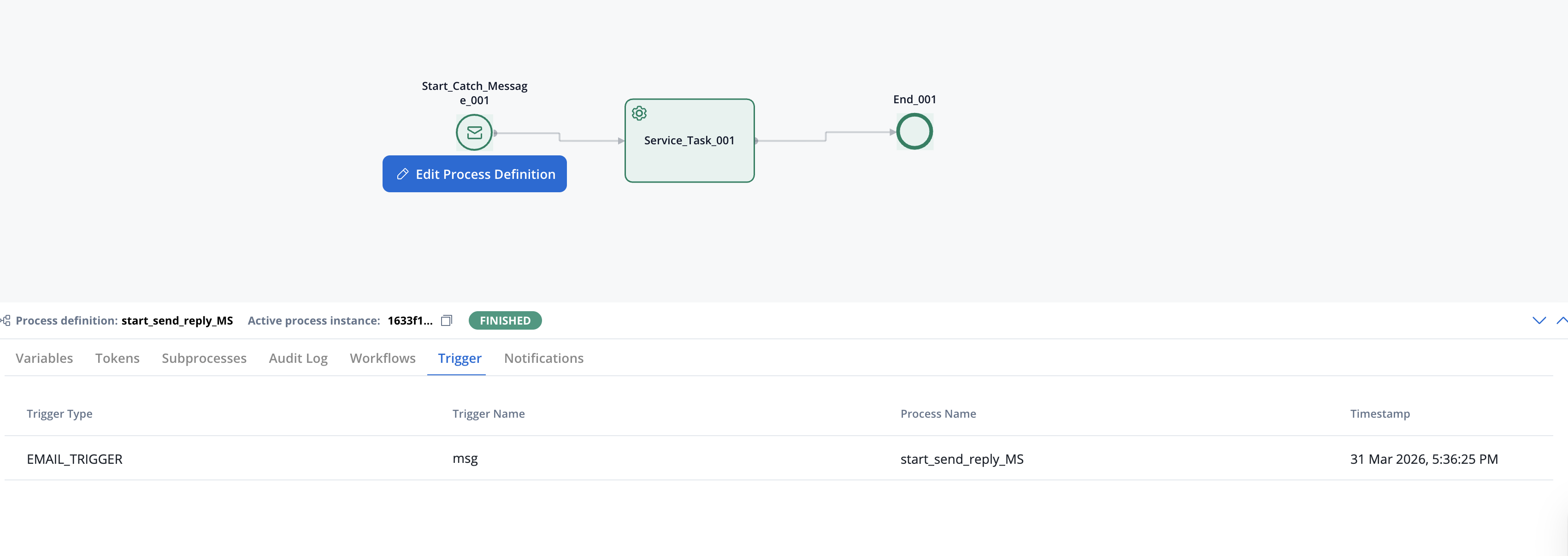
EMAIL_GATEWAY_IMAP_POLLING_INTERVAL). Each polling cycle processes up to 50 messages (configurable via EMAIL_GATEWAY_MS_GRAPH_MAX_MESSAGES_PER_POLL). Emails with the same timestamp as the last processed email are deduplicated automatically using their internet message ID.Sending emails (notification template)
To send emails from processes:Link to a notification template
Add a Send Notification action
Replying to received emails
Microsoft Outlook supports replying to emails received via the Read scope, maintaining the original conversation thread in the recipient’s inbox.Configure the Send Notification action
Set the Reply to Email Header
emailMessage.headerParams). This is required when the reply toggle is on.x-ms-graph-message-id header from the original email to thread the reply correctly. If this header is not available, the system falls back to the standard Message-ID header and looks up the original message via the MS Graph API. Sent replies are automatically saved to the Sent Items folder.Email data schema
When an email triggers a process, the following data structure is available in your process variables:Schema fields
| Field | Type | Description |
|---|---|---|
subject | string | Email subject line |
dateTime | string (ISO 8601) | Timestamp when email was received |
sender | string | Sender’s email address |
body | string | Email body content |
fileAttachments | array | List of attachment metadata objects |
fileAttachments[].filePath | string | Storage path in Document Plugin |
fileAttachments[].downloadPath | string | API path to download the file |
headerParams.Message-ID | string | Standard email message identifier |
headerParams.x-ms-graph-message-id | string | MS Graph message ID (used for replies) |
Managing triggers at runtime
Manage Triggers
Navigate to Runtime Settings → Manage Triggers to view and control Microsoft Outlook email triggers.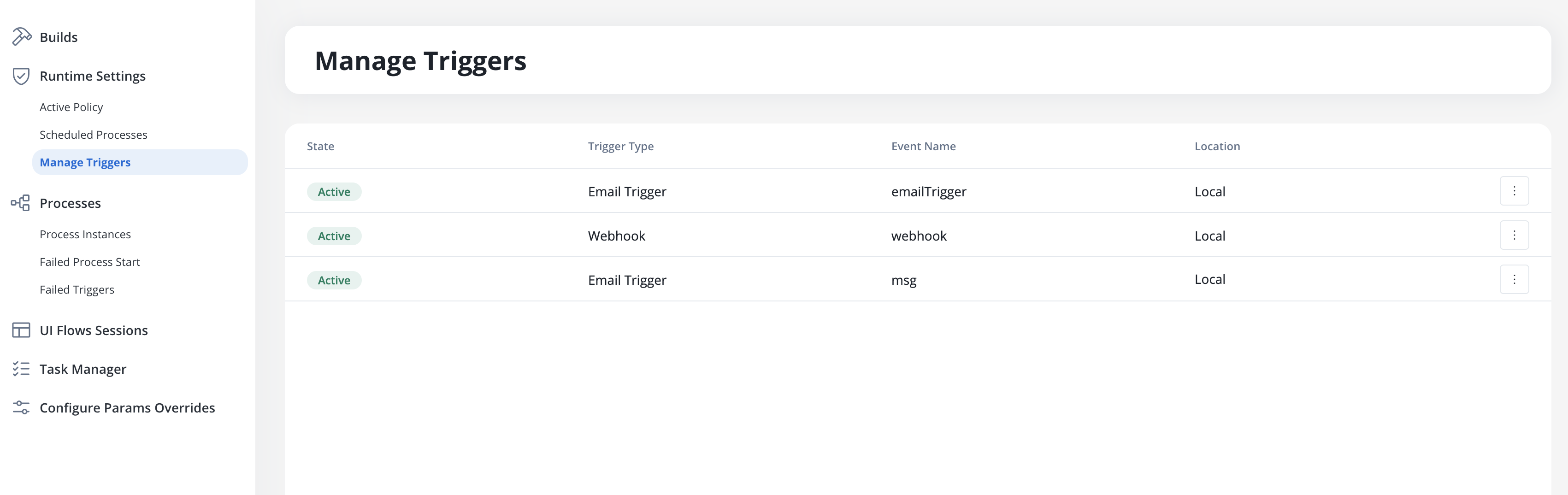
| Column | Description |
|---|---|
| State | Current status: Active or Inactive |
| Process Name | The process definition linked to this trigger |
| Trigger Type | ”Email Trigger” for Microsoft Outlook email triggers |
| Event Name | The Microsoft Outlook data source name |
| Location | Project and branch information |
Activation requirements
For a Microsoft Outlook trigger to appear in Manage Triggers:- Microsoft Outlook data source must be created with Read or Read & Send scope
- Data source must be linked to a Message Start Event node
- The process must be part of a build in the Active Policy
Failed Triggers
When emails fail validation or processing errors occur, they appear in the Failed Triggers section under Runtime Settings. Failed triggers display the timestamp, trigger name, cause type, context (e.g., sender address), and detailed error messages. Click a row to open the details page with full diagnostic information.Common failure causes
- File type not permitted
- File size exceeded
- File count exceeded
- Authentication failure
- Missing permissions
{filename} could not be uploaded because it is not on the list of permitted file types.”Resolution: Update the Allowed File Types in the data source Settings tab, or ask the sender to use an accepted format.Use case: document processing with auto-reply
This example walks through a complete email-triggered workflow: an email with an attachment arrives, the process extracts and classifies the document, then replies to the sender with a confirmation.Create a Microsoft Outlook data source
documents@company.com). Set attachment validations to accept PDF and DOCUMENT types with a 25 MB size limit.Design the process
emailMessage.Access email data in downstream nodes
Process the attachment
fileAttachments[].downloadPath to retrieve the file from the Document Plugin for classification, data extraction, or storage.Reply to the sender
emailMessage.headerParams. The reply is threaded under the original email in the sender’s inbox.Best practices
Use configuration parameters
Set appropriate validations
Monitor failed triggers
Use least-privilege permissions
Mail.Read instead of Mail.ReadWrite if you only need read access.Troubleshooting
Connection test fails
Connection test fails
- Invalid credentials: Verify Tenant ID, Client ID, and Client Secret in Azure AD
- Missing permissions: Ensure the app registration has the required MS Graph application permissions
- Permissions not consented: Admin consent may be required for application permissions
- Expired client secret: Generate a new client secret in Azure AD
Emails not triggering processes
Emails not triggering processes
- Does the data source have Read or Read & Send scope?
- Is the trigger Active in Manage Triggers?
- Is the correct mailbox folder configured?
- Do incoming emails pass attachment validation rules?
- Review Failed Triggers for error details
Emails not sending
Emails not sending
- Does the data source have Send or Read & Send scope?
- Is the data source linked to a notification template?
- Is the notification template’s Email Server set to Predefined Email Connection?
- Does the Azure AD app have
Mail.Sendpermission? - Review process instance logs for error details
Permission errors
Permission errors
| Scope | Required permission |
|---|---|
| Read | Mail.Read, Mail.ReadBasic, or Mail.ReadWrite |
| Send | Mail.Send or Mail.ReadWrite |
- Permissions are set as Application (not Delegated)
- Admin consent has been granted
- The app registration is in the correct Azure AD tenant